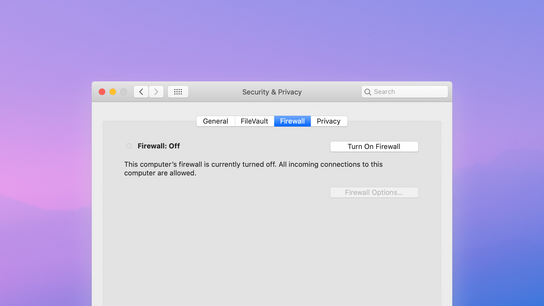
Microsoft was under constant criticisms for not enabling the Windows XP firewall by default. Yet Apple seems to get away scot-free with following in Windows XP’s footsteps by not enabling the firewall by default on Mac.
Microsoft included a firewall in Windows XP in October 2001 but did not enable it by default until August 2004 with the release of Windows XP Service Pack 2. The decision to turn the built-in firewall on by default came after a series of serious and widespread security incidents and attacks plagued the operating system in 2003–2004.
The benefit of hindsight and the timeline here shows us that Microsoft could have avoided the security debacle and protected their users proactively years before it became a serious issue for their customers.
Apple seems to have learned the wrong lesson from Microsoft when it comes to proactively protect their user base. As there’s currently no known security problem with leaving the firewall off, they leave it off; waiting for an issue to appear and start attacking their customers before taking action.
Macs are sitting ducks allowing all packets unhindered to be delivered to all services on the machine. With a firewall in place on every Mac, Macs would become less appealing targets to attackers. Almost all network services are disabled by default on Mac.
However, after leaving a user with a Mac system for a few days – more and more services listening to the network are bound to appear as the user gets comfortable with the new system.
The Mac firewall isn’t an inconvenience to users. It automatically allows code-signed applications (anything from the Mac App Store or other Apple-trusted developers) to bypass the firewall.
Unsigned applications bring up a dialog asking the user to allow them to listen for incoming connections. Notably, the default answer in this dialog is “Allow”; breaking with security software design traditions which usually opts to defaulting such dialogs to “Deny”.
The router standing as a gatekeeper in IPv4-only networks in homes and small businesses is becoming less of a security measure with the ongoing deployment of IPv6. It’s a well-known problem that IPv6 networks, where routers with their port forwarding and firewalling take a step back from their gatekeeper duties, give every machine its own public address and direct connection to the public internet.
The lulling sense of security provided by household routers handed out by internet service providers is becoming dangerously deprecated. Only high-end routers offer IPv6 firewalling as its a more resource-intensive task than IPv4 firewalls. Each device should ideally have its own firewall to protect against attackers on the public internet, and even from other machines on the same local network (or café Wi-Fi.)
iOS has the same built-in firewall as Mac OS X, but it has been disabled in the kernel. Apple would have to rebuild the kernel and send out an update with a new kernel to enable the firewall on their mobile and tablet devices.
An iOS firewall could share the same auto-configuring behavior as its Mac counterpart to avoid inconveniencing users. While it’s harder to imagine an attack for these devices that don’t have any listing services open to the internet, it would help lower the potential for a future attack.
Apple is said to announce updates to its Mac OS X and iOS operating systems at their World Wide Developer Conference (WWDC) next week. The internet rumor mill has it that Apple will focus on quality instead of new features.
I hope they’ll turn the firewall on by default in the next iterations of their operating systems. There would probably not be a big announcement about this on stage at their main keynote event, but the firewall could still be silently switched on to reaffirm Apple’s stance on security.
Update (): Two years later with MacOS 10.13 due to release in another two months, there are still no signs that the firewall will be enabled by default.